Yeah, yeah, I know I’m a little bit pesao with the cryptomonedas and their attacks, but they keep surprising me. There are clearly many more vulnerabilities and attacks in the world: to different softwars, to systems, to connected cars, to Internet of Things devices, to mobile phones… but this kind of attacks on cryptomonedas still surprise me for how imaginative they are. On this occasion, a cybermalote has taken advantage of an error in the code of Bitcoin Core to steal $15,000. And yes,
w «target =» _ blank «> recently cybercriminals stolen in a casino after getting access to the slot-bitches machines through an aquarium thermometer that was in the casino and that was connected to the Internet (spectacular, isn’t it?), but the attacks to steal cryptomonedas are not left behind in terms of imagination and sophistication… that is, that The bad guys know where the money is and they want to steal it., that of violating the security of a mail server to send emails It’s not that funny and it’s not that lucrative.
What is Bitcoin Core?
A few days ago we were urged all users of the Bitcoin Core software to update urgently for an error that could cause a Service Denial in the application, that is, it was closed and it stopped working. Bitcoin Core is one of the first software that came up to manage your cryptomoneda portfolio, but in addition to that it works as a node of the Bitcoin network, so your computer will download a copy of the entire block chain and store it on your computer including every new transaction and you will form
so part of the network and the ‘chain of custody’. It is by far the most used software to store cryptomonedas I use it to save the cryptomonedas I don’t have in an Exchange. We’ve already talked about the various possibilities of storing cryptomonedas, so go through the past items if you’ve come here and you don’t know very well what we’re talking about..
The double-spending bug
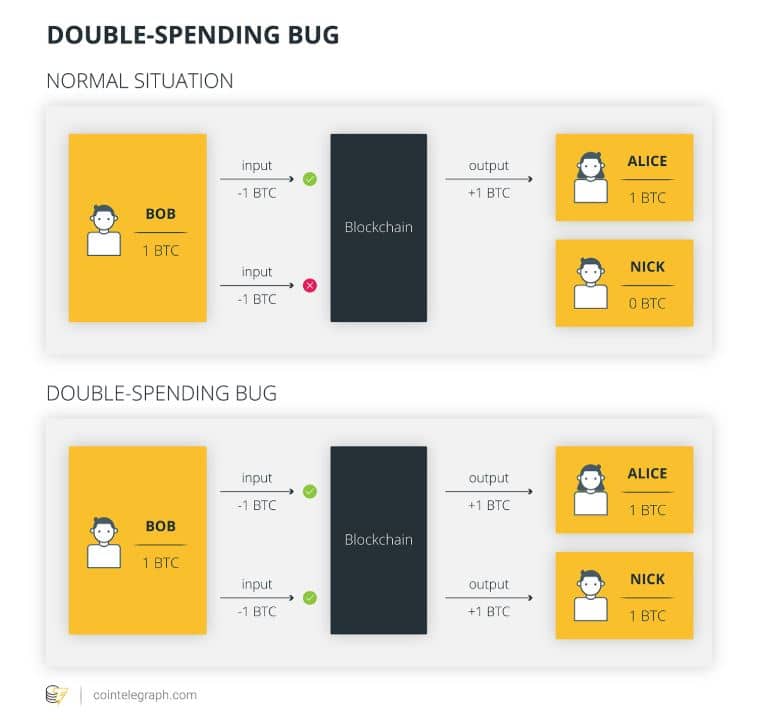
The bug itself did not seem to jeopardize your crypt- savings… a problem in a duplicate input validation could cause the program to fade… great, so we’re up to date and ready. If any of you have programming knowledge and want to know more about the problem of validation of the double-spent (CVE-2018-1744), I recommend this spectacular analysis of Jimmy Song. But as most of the readers of this blog (5 of the 7) are not familiar with programming, we will ex
fold it in a simpler way: basically Bitcoin transactions could be run in a lawful manner, that is, the network allowed if Bob has 1 BTC and I want to sell it, I can send it to Alice and Nick and the network will rule out the transaction that is not complete. So the transactions go a lot faster because they just refuse the completed ones, you don’t have to wait for Nick to tell me he doesn’t want my Bitcoin to then send it to Alice:
The problem is much more serious than it seems since this bug allowed malicious miners to inflate the in circulation Bitcoins simply using this double-spending… but this could have been catastrophic to the network, so the developers decided to keep it a secret (I’m not tired of saying it again: security by darkness NUNCA is a good idea). It was published once vulnerability had already been resolved and when most of the nodes in the network had been actuali
with the excuse of denial of service… but the update was not fast enough to prevent a malote I could blow it up.
The attack: deceiving the network saying that there are twice as many monends that there really are
On September 26, one of these ‘potential malicious miners’ took advantage of the error of double-spending to create 240 million coins from a cryptomoneda called PINGEONCOIN (PGN), the value of which is approximately $15,000. Why PGN and not Bitcoins? Because PGN didn’t have the updated software yet. The cybercriminal He managed to generate all these coins and sold 50% of the 240 million, he couldn’t sell them all because deposits and withdrawals were frozen in a preventive manner by detecting the huge number of coins that were moving.
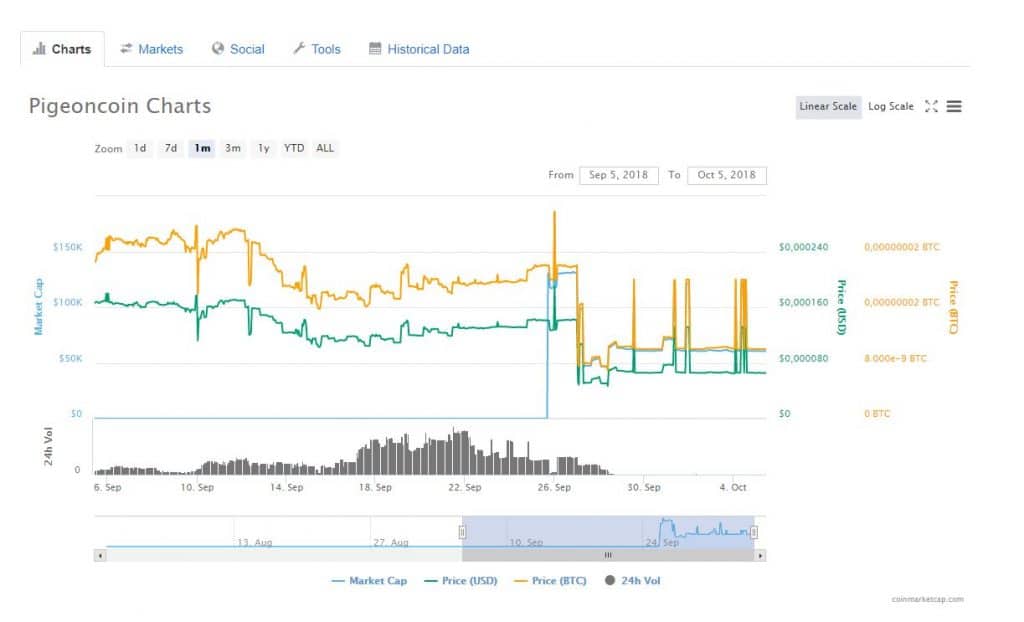
You don’t have to say this. had a brutal impact on PGN, which lost 22% of its value in a few hours and at this time is at the minimum possible value, 1 satoshi (about $0.000067):
And it brings us back to the importance of updates, although on this occasion we could not have avoided the attack on the network.