A few months ago, back in January, the bad guys hacked an Exchange in New Zealand called Cryptopia and took about 16 million dollars. Yeah, I know you’ve read a lot of news like this and it’s even been on the news, but just as we have on other occasions talked about how the Exchange had an insurance to assume these losses, on this occasion it has not been possible to return from the Security gap and the Cryptopia Exchange has declared itself bankrupt… for what I have
and it’s time to talk about Business Continuity.
All companies know what Business Continuity is. It seems obvious, doesn’t it? are the measures to be taken to ensure that your company is able to recover in the face of an interruption of its activities. This interruption can be given for many causes, not just because hackeen as in the case of Cryptopia… Imagine, for example, that there is a strong snow and employees cannot reach the company and therefore cannot ‘produce’ or develop their activities normally. Or that there was a light cut due to some works being done on the same street.
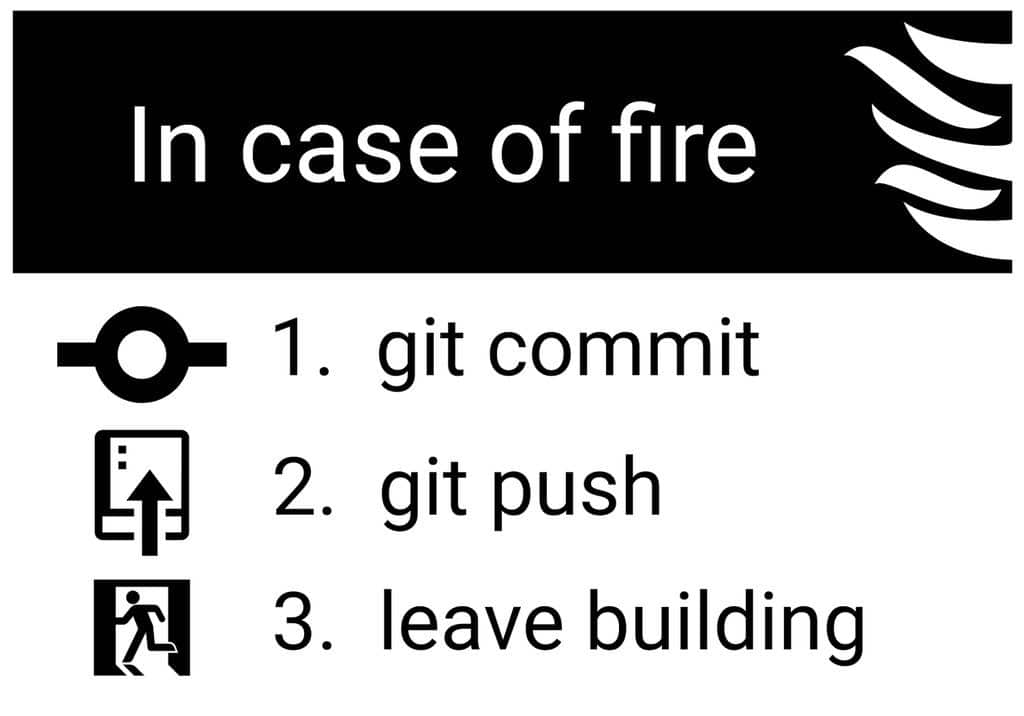
Although Business Continuity sounds like something very ‘IT’, from modern computer or telecommunications companies, actually We have been doing many things for the Business Continuity for a thousand years: from the evacuation test that demands other rules such as the Industrial Risks or the backup of information, redundant lines of light or Internet connection, etc.. A few years ago I went to a day on Business Continuity and one of the presentations was given by a ship captain of the Spanish Navy, and explained that they have been doing ‘business continuity’ for a thousand years and, in case of a threat in a subma
rino (as a waterway), you know exactly what you have to do so that the mess doesn’t go to the bottom… and that’s also continuity of your business.
What is a Business Continuity Management System?
This is Just… to translate all this into a continuous improvement plan, the famous Denimg or PDCA cycles (plan-do-check-act) we already know of other standards and ISOs. This way, not only are we going to document everything we do to support our business, but we’re going to try and improve it.… for example, you would know how long it takes to recover a file with your current backup system… but how long it takes to recover an entire server and have it work again in case the original fails? or if our transp company
orts that send the oranges that we produce to our customers fail… do we have any other companies in our contacts that can send us urgently these oranges before our customers get angry? and more or less how long would it take our customers to get angry if these oranges are delayed a little bit? Surely if they are delayed a few hours they are not given or noticed, if they are delayed one day we can have problems… but if they are delayed 3 days they still seek another supplier and we lose the customer, right?
It’s not that simple, but it’s not a complicated process either. We must first examine our business and detect the processes that really make the business work.. It is of little use to have a room full of state-of-the-art servers if our main client sends us orders by Fax and, if that fax is damaged, we would lose a large part of our billing. It seems clear that what needs to be maintained by all means is that fax, right? a risk analysis once the main business processes have been identified.
What has Cryptopia failed to do?
We could identify a number of things that have failed in Cryptopia and led to the cessation of their operations. We don’t have much more information about it, so we’re going to do an exercise of imagination with the information we have:
– Cryptopia took 2 weeks to detect the attack, but during those 2 weeks there were users who lost their cryptosavings: something failed in his incident management (users sure that they protested strongly) and in their safety management (the anomalous fact should have been detected before users realized).
– There were almost two months to solve the security failure: Do you know how many Exchanges there are in the world? Enough to let if in a couple of days your favorite Exchange doesn’t work, go to another. 2 months is totally unacceptable < /
strong >, I would only have kept my account there of having a lot of money in cryptomonedas… and obviously at 2 months when it came back to work I would have taken them out.
– They have not been able to bear the cost of returning the stolen money to the users: this indicates that your insurance policy was not properly configured.
– They have not managed the crisis properly: with good crisis management, Cryptopia should have been back in place A few months ago, either offering discounts on commissions or innovating with some new service…
I don’t know, but something that would have made new users discharge on the platform, which would have made it easier to get back to the economy.
We could probably identify some more points, such as the rules that affect exchanges worldwide and that force them to have a high percentage of their crypto- assets backed by real money… and gives me that Cryptopia did not comply with this regulation at all.
The result: bankruptcy
If last week we were talking about how the exchange Binance had been able to overcome a hacking and return the money to users with a self-supporting fund, in this case we have to talk about just the opposite, Cryptopia has not been able to overcome the stick and has been declared bankrupt. This does not mean that the evil have made it break, they have actually done it themselves not taking the necessary measures to ensure the relatience business,
that is, the ability to recover from a major business interruption.
Do you know how long it would take to reinstall your company’s database server in case it gets damaged? And how long would it take for your customers to get angry if what is ruined is the portal on which the orders are made? How much money would we lose during that time? All these basic questions we could answer if we had an adequate and up-to-date Business Continuity Management System… and of course we would be able to assess the risk of a malot stealing money from our system and what measures to take to detect and stop the attack.