According to Google, passwords are dead and we have to look for other ways to access services. We have talked in previous posts about how to create a good password and how to store and remember all those passwords once generated, which is very good for most users… but sometimes we hear that han hacked some service where I will be
you are discharged and that the malotes have been able to access the user database What happens then? Have you been able to access my user? Well, it depends, users’ passwords are normally stored encrypted in the database and it is only possible to obtain them by gross force, so if we have a robust password they won’t be able to access our user… but on other occasions our password has been exposed, with what without eating it or drinking it we have kept our ass in the air even though we made a lot of effort to generate our password, we have not given it to anyone and we have taken care of it
with the same zeal we took care of the keys to the house… Damn. hackers.
On the other hand, it may happen that we have a precious password, meeting all the security requirements we discussed a few days ago but that we use a computer that has a virus or Trojan (we’ll talk about the Trojans, I’m in) specialized in stealing passwords. In this case, it will not matter whether our password is secure or that it is stored in the service database. the Trojan or virus will capture it as we write it on the keyboard before sending it to the service to be encrypted and stored in the database.
Looks like the bad guys know all about it, huh? I look at the URL’s little candadito as it’s safe, I see you browsing through HTTPS, I broke my horns in generating a secure password… and now it turns out I’ve connected. from a friend’s computer (or from the hotel computer to print my plane tickets) I had no updates or antivirus and my password was stolen.. If you can’t trust anyone!
2FA: Double authentication factor
The double authentication factor It’s gonna solve that problem. Basically, to access a service that supports it, we’re gonna need to a password and a random number that generates our mobile. It seems complicated, doesn’t it? Two things to remember! No, don’t worry, let’s see what exactly this new security functionality does.
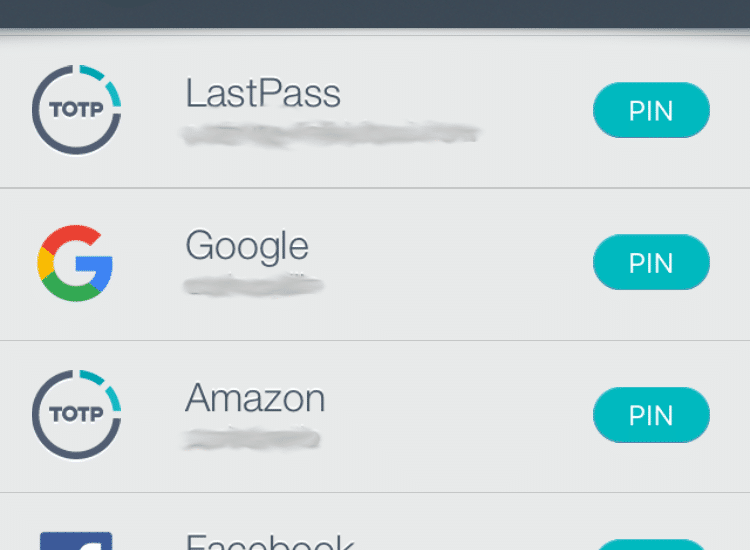
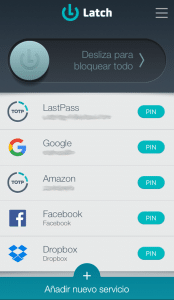
When we discharge in a service that supports 2FA, the service is associated with an application that we install on our mobile to manage 2FA access. Every time we want to get in from a rare location (No, he doesn’t ask every time.), we have to enter the application of the mobile and write the number you have generated at that time, which is usually 6 figures and for a certain duration. So the service knows it’s us (we have our phone, not just the password) and it’s a licit connection. This is an image of my mobile, for example:
When I want to enter one of these services, in addition to writing my password, the system asks me about the number that at that time has generated my phone:
The good thing is that this functionality is very configurable you can, for example, make Facebook ask you for the number only when you connect from a computer or mobile that is not your usual or from a rare country that is not the usual. Only in that case will the number have to be written.
What services do 2FA support?
New services that support 2FA are gradually being incorporated, but we can find it already available in the most common ones. Not all of them have the possibility of ‘centralizing’ the PIN in an application, some simply send it by SMS to your phone (and by the way they are done with your phone number, so they know you’re a network-faithful user). I mean, you can use 2FA on Google (https: / / www.google.com / landing / 2step /), in Dropbox (
ener noreferrer «> https: / / www.dropbox.com / help / security / able-two-step-verification), in Amazon (https: / / www.amazon.com / gp / help / keeper / display.html? nodeId = 201962420), of course in LastPass as we already commented (https: / / helpdesk.lastpass.com / multifactor-authentication-options /), in Microsoft (https: /
/ support), on Facebook (https: / / www.facebook.com / help / 148233965247823), on Twitter (https: / / support.twitter.com / articles / 20170388 #), in Instagram (https: / / www.turnon2fa.com / tutorials / turn-2fa-instagram /… and in many more services, I use it even in services like GitHub (
/ help.github.com / articles / providing-your-2fa-authentication-code / «target =» _ blank «rel =» noopener noeferrer «> https: / / help.github.com / articles / providing-your-2fa-authentication-code /).
Come on, you convinced me, what do I have to install on my cell phone?
There are several applications capable of identifying the services and generating the number, the most common is surely Google Authenticator (available for iOS and
ticator2% 26hl% 3Des & usg = AFQjCNFKPVZES2zzpNQFkUtpCbyWgjm3yw «target =» _ blank «rel =» noopener noeferrer «> for Android). In my case, I use Litch of the ElevenPaths because it gives me some more flexibility and because I already had other integrated services with Latch, so having everything in the same application is very comfortable. However, if you want to start from the beginning, the easiest thing is to access to Google’s manual and follow the steps to have a little more secure your GMai account
l. Once you have the first given of discharge, you will come up with other services to protect and I’m sure you will get a little bit of a double-factor- to authenticate all your services.
Come on, encourage yourself that it’s very simple to do and with that we exponentially increase the security of our user. No one could access that protected service, not even having our password!




[…] todas tus contraseñas en un gestor al que solo tú tienes acceso con una clave muy difícil y doble factor de autenticación, nadie podrá tener acceso a dicho repositorio si tú no estás. Ni aunque tu mujer o tu hermano o […]